Hey there.
Here’s the second part of this exceptionally bi-weekly newsletter. Why two parts?
Because the Foundation for Defense of Democracies (FDD) just released a report on an investigation that I contributed to, along with Max, Ari, Sam and Paul. When I landed in the U.S., they were the first persons that I ‘e-met’as we say. I am grateful to them to have let me join a team that I like to describe as a modern adaptation of “the Famous Fives”.
It’s time now that I present you the main findings of this report, uncovering a persistent activity from Spamouflage aka Dragonbridge Chinese threat actor targeting the U.S. audiences. If you are not familiar with it or you need to freshen up your memories, this actor has been heavily investigated by Graphika, ASPI and Mandiant since 2019.
This report is a small contribution to the observation of the evolution of TTPs, but I hope you will find some of the TTPs we describe interesting!
What to expect:
Nota Bene: the next edition of this newsletter will resume on Thursday April 11 to give the author a bit of time after publishing twice in the last week.
A Modern Adaptation of the Famous Fives
So, when I arrived in the United States, a bit lost and confused about what was going with countering FIMI, I soon met Max. Max is today a Senior Analyst on Emerging Threats at the Foundation for Defense of Democracies (FDD), but at the time, he was a bit like me, looking for places where he could make an impact in terms of identifying FIMI threats and developing public recommendations.
He quickly told me that he had an investigation going on with three other investigators, Ari, Sam, and Paul. I was thinking, is this some kind of modern adaptation of “The Famous Fives”, except we are not teenagers anymore and computers have replaced outdoors adventures?
According to them, there was something dodgy going on targeting the U.S. audiences, with high suspicions that it came from actors affiliated with China.
Max asked me if I could take a look at it, if I had time of course. Time, yes, I had plenty while waiting impatiently for my work permit.
He thought he had to add a few words in French, with his strong American accent, to persuade me, but I was already in.
I started looking at the Facebook pages and accounts. What I was seeing made me smile, reminiscent of patterns I had observed or read about in the past. But soon other signals were worrying. The size of the network. The narratives. The potential targets.
And soon I found myself joining their team to dig further, as most as we could, with this tricky Facebook platform which likes keeping its secrets for itself.
Before I present our findings, I just want to thank this team for letting me join them so spontaneously. It is what makes this work quite enjoyable, combining our perspectives, skills and past experiences to observe and analyze current intriguing activities.
Although being the only girl was sometimes tough to understand all the geek nerdy references, our conversations and investigations definitely helped smooth the landing in the United-States.
Spamouflage, Old and New TTPs
So, what did we find?
The threat attack pattern of Spamouflage
The network we uncovered behaved like the Chinese-affiliated threat actor known as Spamouflage aka Dragonbridge. This actor has been heavily investigated by Graphika, ASPI and Mandiant since 2019. It is a huge network, active on multiple platforms with targeted audiences across the world. Just in the latest months, the network has been reported targeting Canada, the U.S., but also Taiwan, Australia, Britain, Japan, and global Chinese-speaking audiences according to the latest takedown by Meta last summer.
The network we observed was active on Facebook and was composed of pages and accounts which had created their own echo chamber:
The pages, acting as influencers in different domains (arts, blogs, music etc.) had typical, and less typical, English-speaking names. They posted most of the time apolitical content. They were also sometimes inactive for a while. Then, suddenly, reacting to current events or active crises, they published partisan political content about U.S. domestic politics or U.S. foreign policy. After a few days, they would change back to apolitical content, hiding the previous timeline, or would go back to inactivity.
This behavior was a first hint that it could be Spamouflage.
The accounts, bearing English names or Southeast Asian names, spoke sometimes in English, sometimes in Chinese, commented the pages’ publications and shared them across this echo chamber. The comments generally amplified the narrative propagated by the publication. The accounts commenting were constantly the same on each publication, all commenting in the same period of time. When looking at the accounts’ past activity, some of them seemed to heavily post or comment negatively about Guo Wengui, the anti-CCP businessman in exile. Guo Wengui has been a persistent target of the Spamouflage network.
This past activity and target was a second hint that Spamouflage could be behind it.
Looking at the narratives spread within this echo chamber, it was highly reminiscent of the narratives observed in one previous report by Graphika, published after the U.S. 2020 Presidential election. American failures, Chinese achievements, US-China Rivalry were all themes that we observed being pushed by the network. These themes were of course updated with modern concerns, such as the state of the American economy or the current Israeli-Palestinian conflict. The audiences seemed to be both English-speaking and Chinese-speaking communities as well, probably ones living in the U.S.
The narratives were a third hint that Spamouflage could be behind it.
All together, we concluded with high confidence that Spamouflage was likely the actor behind these FIMI activities. But that’s not it; we found more new interesting things.
An increased industrialization of Spamouflage operations
Firstly, we noticed signals that some accounts may be generated through the use of an application programming interface, suggesting that the operators have a streamlined, automated process for generating accounts. For example, five profiles have an original profile photo displaying the error message “We couldn’t find the photo” with the URL of Unsplash, demonstrating the failure of an automated pull.
Secondly, while it had been noted in the past that Spamouflage hijacked accounts on Twitter, we found that Facebook accounts were also potentially hijacked. They appear to be genuine accounts repurposed to push Spamouflage’s narratives.
Thirdly, we found indications that ChatGPT or a similar machine translation tool might have been used to improve the development of text-content. Many accounts’ comments featured quotation marks on a separate line below the final sentence. If you try translating something in ChatGPT, the answer is always given within quotation marks. It could mean many things, either hasty posting without proofreading or the use of automated tools to post. For sure, it is a sign that there is a will to increase text-based content credibility through the use of GenAI.
Fourthly, not necessarily new but adding to the previous comment, AI-generated images were used to create some of the accounts’ profiles, demonstrating also a search of credibility for imaged-based content. However, the content delivered remained unsophisticated. Videos were mostly cheapfakes while the text content was directing to mainstream U.S. newspaper.
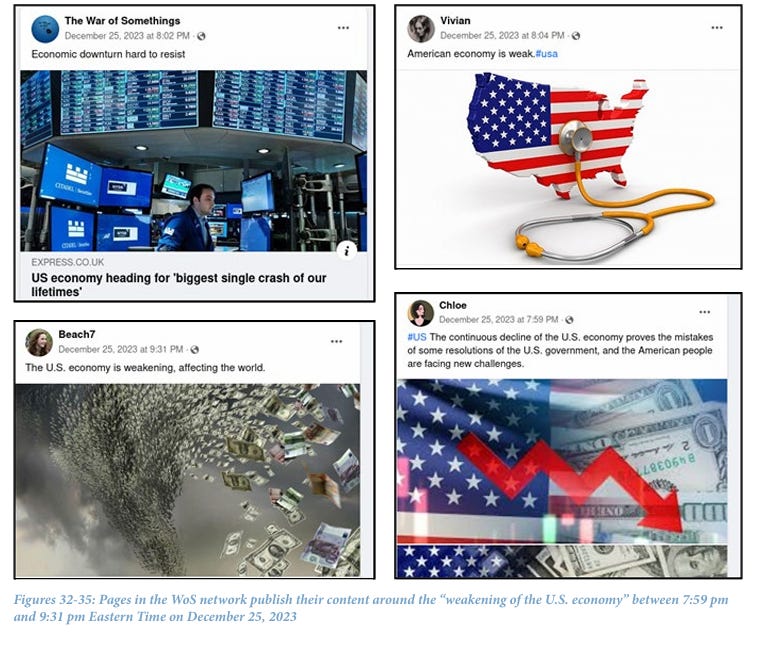
Lastly, looking at the timing of posting of pages and accounts, we found that this echo chamber was operating between 7.50 pm and 5.00 am Eastern Time, with breaks between 11 pm and 12 am. This timing corresponds to 8:50 am to 6:00 pm in Beijing, with a lunch break between 12 pm and 1 pm, from Monday to Saturday. I am not kidding, it really looks like a business activity.
So what, you may ask?
After the recent report of ISD documenting the activity of Spamouflage on Twitter targeting the U.S. audiences, this reports sheds light on another potential Spamouflage operation, with signs of a professional activity and increased sophistication for maximum credibility.
What is positive is that, as noticed many times in the past with Spamouflage, the network did not break out of its echo chamber… yet.
What is indeed concerning is that all these detected assets, as well as many others we continue to discover, look like they are prepositioned.
Many pages and accounts have been recently created, in the last months. They share similar characteristics, similar names, and look like a zombie army.
As we know that the Chinese actor has an ability to quickly catch up with its competitors, what will it look like once these accounts and pages are all activated?
For all the details and recommendations, you can find the report here.
Your Press Corner
Here’s the weekly readings to keep you connected to all the conversation on global elections and information operations:
China’s Advancing Efforts to Influence the U.S. Election Raise Alarms - The New York Times (nytimes.com) - and in case you want more of what I just explained, here’s the NYT covering the report!
Life After Death? IO Campaigns Linked to Notorious Russian Businessman Prigozhin Persist After His Political Downfall and Death | Google Cloud Blog - Throughout 2023, Mandiant has observed shifts in the activity from multiple IO campaigns linked to Prigozhin, including continued indicators that components of these campaigns have remained viable since his death.
Czechs sanction Medvedchuk, website over pro-Russian EU political influence – Euractiv - The government’s sanctions list said Medvedchuk used the firm and Marchevskyi “in multiple EU member states for financing cooperation with journalists and for covert financial support for selected individual candidates in the European Parliament election, with the aim of supporting the foreign policy interests of the Russian Federation.”.
Disinformation targeting Brigitte Macron spreads beyond France (france24.com) - From France to the US. For once, it is the other way round that malign influence spreads. And at the heart of it, the role of translators…
Gendered Disinformation Is Not a “Women-only” Issue, It Poses a Threat to Election Integrity – Georgetown Security Studies Review - A great analysis on an important part of these information manipulation activities.
Deepfakes with Chinese Characteristics: PRC Influence Operations in 2024 - Jamestown - On China integrating AI in its cognitive warfare.
Beware of Tinder dates spying for Putin, German tourists in Russia warned (yahoo.com) - Maybe we are finally going to be able to use T0104.002/Date Apps in our investigation!
Canada's elections watchdog struggles to investigate foreign interference allegations, inquiry hears | CBC News - Inquiry also hears that CSIS told election chief of possible meddling in Don Valley North nomination.
New Hampshire House passes AI election rules after Biden deepfake | The Hill - on countermeasures against deepfakes.
Amazon will have to publish an ads library in EU after all | TechCrunch - Amazon will have to provide information about the ads running on its platform in a publicly accessible online archive after all, following a decision by the European Union’s highest court Wednesday.
Writing with Invisible Ink: Russia's Newest Disinformation Tactic (alethea.com) - A new TTP in Russian IOs, according to Alethea, has been observed to avoid detection from platforms.
Slovak team develops world's largest fact-checking database in battle against - spectator.sme.sk - IVAN SRBA and his colleagues from the Kempelen Institute of Intelligent Technologies (KinIT) are among those leading efforts to increase quality of online content and prevent spreading hoaxes and untruths and have created the world’s largest database of checked facts in the world and an app for media professionals to verify information, regardless of what part of the world it originated in.